Zoom vulnerability for Mac users
Office of Information Technology
A vulnerability published earlier this month informed Mac users worldwide that the Mac Zoom Client allows any malicious website to enable your camera without your permission. Both Apple and Zoom have since responded to this vulnerability by releasing updates.
If you use Zoom (or one of its white labeled products RingCentral or Zhumu) on your Mac, you may have already been prompted to update your software. If you’re not sure, and would like to test for this vulnerability, follow these steps:
- Open the “Terminal” application
- Enter the following command: lsof -i :19421
- Press return/enter
If that command returns nothing but a new line, your system is ok. However, if that command returns output similar to this:
COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME
ZoomOpene 1471 ksf1 3u IPv4 0x6ad96503eb75625 0t0 TCP localhost:19421 (LISTEN)
your system is vulnerable and needs to be updated.
Here’s how to update Mac Zoom:
- Navigate to your Applications folder and select “zoom.us”
- Double-click to open it
- As the software launches, it should prompt you for an update:
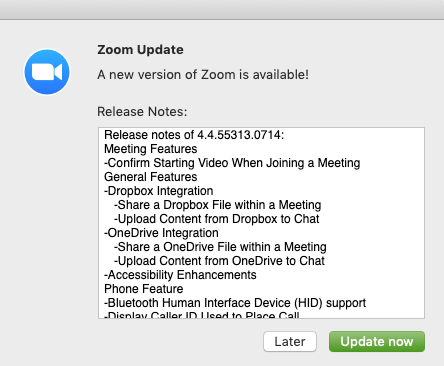
- Click “Update now”
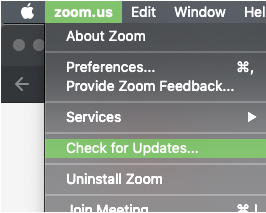
If you don’t get prompted, and you’d like to check for updates, simply go to the Zoom menu and click File > Check for Updates:
Zoom on Other Operating Systems
Zoom users on other platforms may also be vulnerable if their browser automatically opens the software without asking. Improve your online safety by updating your browser regularly.
As always, if you need further assistance, contact your local Service Desk!
